17 Aug Understanding Cloud Computing Data Security and Compliance
In this post we will help you understand the risks and offer best practices for cloud computing data security.
Threats to cyber security are increasing and it has become a top priority for most businesses in the U.S. “The year 2020 broke all records when it came to data lost in breaches and sheer numbers of cyber-attacks on companies, government, and individualism” said a recent Forbes article.
Cloud Computing Data Security Definition
What is data security for cloud computing? Cloud security is simply the tools and practices used to protect cloud assets from cyber attacks, leakage, deletion or data-loss due to natural disasters. In most cases the term “cloud security” refers to protection against cyber attacks against cloud resources. Cloud security may include everything from firewalling, encryption, monitoring, user policies and back-ups and recovery.
Related: The Difference Between Cloud Computing and Cloud Storage
Common Challenges
Data loss or leakage is the top cloud computing data security concern in 2021 according to Statisa.com survey results. In fact, 64% of respondents identified data loss as a top concern. When securing internal cloud or acquiring cloud services, the challenges listed below should top your list of challenges to address.
1. Data Breaches
Companies that experience a data breach may face serious financial impacts as a result of breach. This can include everything from loss of customer trust and loss of intellectual property to decrease in market value, regulatory fines, legal or contractual liabilities and incident response expenses.
2. Configuration and Change Control
Misconfigured cloud security can result in errors, data loss and exposure to malware, breaches and more. Change control is also important to ensure a company doesn’t experience downtime or risk exposure to cyber threats during a transition to the cloud. It is critical to consider data continuity and other GRC best practices as a top priority when going cloud.
3. Cloud Security Architecture and Strategy
For an effective cloud migration strategy, businesses need cloud security architecture expertise and an upfront strategy. As businesses adopt SaaS and IaaS, it is critical to include an overarching security framework tailored to the cloud. It is not enough to simply port existing IT security controls to the cloud.
4. Identity, Credential, Access and Key Management
It probably comes as little surprise that cloud computing presents a considerably more challenging security job over traditional on premises technology, especially where identity and access management is concerned. Multi-factor authentication, monitoring and tracking are vital.
Simplify Your Path to Secure Cloud
CyberlinkASP’s Virtual Desktop Hosting and Application Delivery Service provides secure, affordable, and scalable cloud hosting.
Cloud Computing Security Best Practices
The following cloud computing data security best practices will help you address the challenges above.
Plan and Policy
A robust cloud security strategy should include accountability and ownership concerning cloud security risks, compliance, identity controls, monitoring and audits.
Identity and Access Management and Privileged Access Management
Use holistic identity verification and authentication tools and processes to protect cloud hardware, software and data. Limit exposure by only exposing infrastructure to the internet where and when it is explicitly necessary and creating role-based access to different levels of your infrastructure.
Identify All Cloud Resources
With today’s easy access to requisition cloud tools, shadow IT and the like, there may be points of exposure unknown to your cloud security team. Discovering and grouping all existing tools being used is critical to bring them under the cloud security policy. It’s important to eliminate those solutions being used that don’t comply with policy.
Password Control
It should be common knowledge at this point that sharing passwords is a no-no, but it is up to IT security teams to assure that this policy is being strictly adhered to. Identify any credential management tools that users in the organization may use to confirm that these tools comply with security policy.
Vulnerability Monitoring
Regular scans and security audits should be performed to identify and patch potential vulnerabilities.
Encryption
There are a variety of encryption tools on the market. Be sure your cloud vendors and internal cloud are using solutions that adhere to the highest industry standards while data is both at rest and in transit.
Backup and Disaster Recovery
Be sure all of your cloud vendors, whether public shared or private dedicated, offer backup and disaster recovery policies that align with your policy and meet the highest industry standards.
Monitoring, Alerts, and Reporting
Network security and monitoring is critical to data security in the cloud. Your cloud vendors should offer 24-7 security monitoring and you should requisition security monitoring vendors and solutions to monitor your private cloud.
Ensure Data Availability
It may be obvious, so we will just mention this quickly–data availability is one of the key benefits of cloud. When choosing cloud providers, be certain they offer an uptime guarantee above 99% in their service level agreement. A rock solid backup and restore policy is also critical to data availability.
Data Integrity in the Cloud and How to Preserve It
Data integrity is among the most critical components of cloud data security. Lack of data integrity can lead to inaccurate forecasting, client data exposure, compliance problems and more. Preserving data integrity includes preventing fraudulent, malicious or simply unauthorized changes or deletion of a business’s data.
Compromised data integrity is often caused by human error, internal fraud, malicious attackers, faulty or compromised hardware, transfer errors or even cloud configuration problems.
You may also be interested in: Defining Cloud Governance
User access controls and traceability are critical to the audit process that help to ensure data integrity. Data integrity is yet another reason why access controls are so important to cloud data security including monitoring for failed login attempts and strict controls over who can modify and delete data.There are software solutions available to help preserve data integrity. These solutions include tools that work constantly to compare current data to the last known good data state. Inconsistencies are flagged by the solutions.
Data Confidentiality in the Cloud and How to Maintain It
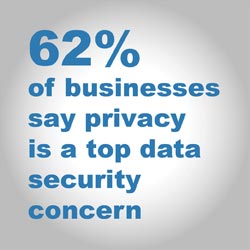
Data privacy was identified by Statista as the second top priority concerning data security with 62% of respondents citing confidentiality as their chief concern.
Whether you are concerned with HIPAA, GDPR, ABA or other common data privacy compliance requirements, or you want to protect your company’s intellectual property, confidentiality is vital to continued success in the cloud.
Related Reading: The Importance of Law Firm Cyber Security
To maintain data integrity, you have to know your data and categorize so that you can prioritize it by sensitivity. Categorizing and classifying your data and knowing where it is stored will help you set appropriate security controls and set the right user controls.
Other basic protections like data masking and encryption are key to maintaining data confidentiality. According to Wikipedia, “Data masking or data obfuscation is the process of hiding original data with modified content The main reason for applying masking to a data field is to protect data that is classified as personally identifiable information, sensitive personal data, or commercially sensitive data.”
Conclusion:
Data security is a growing concern for all businesses. While cloud computing has been proven to be more secure in most cases than on premise systems, there are more attackers and more malicious software created all the time. When it comes to cloud data security, choosing a cloud services provider with a solid reputation and services like round-the-clock monitoring is the first step to assuring cloud data security.
Key concerns for internal cloud data security:
-
Plan and Policy
-
Identity and Access Management and Privileged Access Management
-
Identify and Categorize All Cloud Resources
-
Password Control